Ozark Debt Settlement

There are countless reasons why a person accumulates a huge amount of debt. It’s normal for people to need financial advice at some point in their lives. If you suddenly lost your job, had a personal loss, or suffered from a bad investment, dealing with debt can be a heavy burden to bear, especially if you’re earning just enough for your daily needs.
Our certified debt settlement experts know that even if you’re deep in debt, you should still be able to continue living your life. We’ll do the negotiations with your creditors to help you reduce the total amount of your debt. We’ll see to it that you’ll be paying a lower monthly payment or a fewer number of total payments. We won’t eliminate your debts by getting you a new and bigger loan. Our main goal here is to eliminate your debt through effective negotiation and debt settlement.
Our process starts by evaluating your overall debt and your current financial status. If you’re simply tired of verbally-abusive phone calls and daily struggles to make ends meet, we will find the right solution for you. Optimal Debt Solutions is here to help Ozark, AL residents find the best debt solution so they’ll be able to gain financial freedom and live with fewer worries.
Call Optimal Debt Solutions today at (205) 784-1723 for your Free Evaluation!
Effective Ozark Debt Relief Program

The first step is to have our certified debt specialist evaluate your current financial situation. We’ll provide a free evaluation for you so we can review your existing debts, financial status, and current payments. We do this to completely understand where you stand when it comes to your current debts and your ability to pay. After completing the evaluation, we’ll give you a savings estimate.
Next, we’ll formulate a personalized debt reduction program according to your needs and current financial situation. We’ll discuss all your debt settlement strategies and start setting you up so you can effectively manage and monitor your debt relief program. We also have an online portal that will make it easy for you to access your debt reduction program and debt resources anytime. You can also communicate with your certified debt settlement experts through the portal.
Once we’re able to come up with the proper course of action based on your situation, we’ll start with the negotiation and settlement process. We’ll be using several tactics and strategies that we usually find useful during this phase. We’ll reach out to your creditors on your behalf and analyze how we should approach them. We know how different collection agencies and organizations handle bad debt, so we can figure out the best way to negotiate with your creditors.
As your debt settlement program progresses, you’ll get direct access to our online portal. Our debt specialists will be available to answer your questions and assist you throughout the whole process of settling your debt. If you want to start settling your debts and move towards gaining financial freedom, Optimal Debt Solutions is the right solution for you!
Settle For Less Than You Owe
Debt consolidation and credit counseling in Ozark focus more on combining several debts, so it will be easier to monitor. Debt settlement is different since it’s focused on reducing the total amount of your debt and the number of monthly payments that you need to complete- so you can get out of debt faster. Debt settlement can be achieved through effective debt negotiation. Debt settlement is considered one of the best solutions for managing credit card debt.
If you’re dealing with credit card debt, unsecured loans, or department store card debt, we can help you find the best debt relief solution. We’ll communicate with your lenders, creditors, and debt collection agencies on your behalf. Unlike credit card consolidation, this method isn’t just getting one huge debt to settle the other smaller debts.
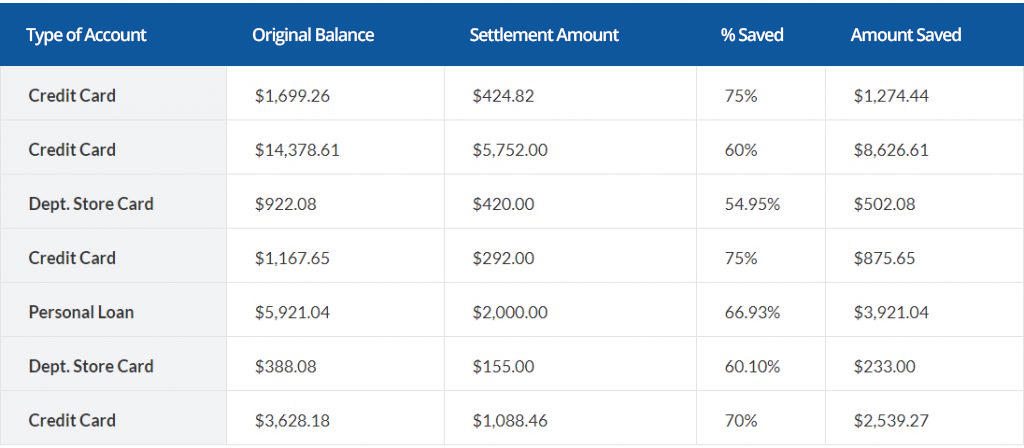
Debt settlement is an effective negotiation of your debts that will result in a debt reduction of up to 50%. Our debt settlement experts will use a personalized approach when we reach out to your creditors. We’ll offer them a payment solution that will work for your current financial situation.
Benefits of Debt Settlement

Debt consolidation, debt settlement, and other debt relief solutions in Ozark can be excellent alternatives to bankruptcy. Instead of hiring a bankruptcy attorney, there are less expensive options like reaching out to debt settlement companies like us. We will help you gain financial freedom by getting full control of your finances again and eliminating all of your debts.
Ozark Debt Settlement Company

Through debt negotiation, our certified debt relief specialists can reduce the total amount of your debt while providing manageable payment plans for you.
Call Optimal Debt Solutions today at (205) 784-1723 for your Free Evaluation!